While cloud computing has long been widely adopted among enterprises, cloud strategies and the levels of cloud maturity differ extensively based on the context of the organisations and investments.
Is your organisation missing out on tremendous benefits cloud computing services can deliver?
These are the most popular cloud services and how they can help your enterprise:
A managed IT service is where businesses choose to outsource the responsibility of managing their IT services and equipment. The managed service provider (MSP) will then charge a monthly fee for what the companies have used.
The upsides of utilising an MSP are flexibility and cost-effectiveness. This method enables businesses to focus more on their core values instead of concerning about IT management chores.
The actual work of an MSP may vary business to business, industry to industry, but typically they would perform everything that a normal IT department would do, including but not limited to:
Normally, the staff at the MSP office are already experts in their fields. Choosing managed services can, therefore, allow businesses to access a higher quality pool of talent than they can ever be able to.
With the ever-increasing amount of digital payments, cybersecurity becomes critical now more than ever. All systems have to be closely monitored around the clock. Yet, they also have to be agile enough for seasonal industries like hospitality and retail. Moreover, managers must ensure their data is frequently backed up, and there is a disaster recovery strategy in place.
In addition to the ongoing tasks, businesses also need to prepare for the future, figuring how new cutting-edge technologies like IoT, AI or Cloud can help them digitally transform how they operate.
But not every business has the budget to invest in an A to Z structure. For them, maintaining the current IT infrastructure is tough enough, planning for future growth is beyond their control.
This is where requesting managed IT services from a service provider can be helpful to lessen your IT burdens.
A good MSP will ensure the business is compliant, safe and secure with up-to-date security patches, firewall, and other security measures. The business will be able to get their hand on the latest IT security software without the need to develop a full-fledged IT team and still be able to compete with other players in the market.
The MSP always stay up-to-date on regulations and industry-specific policies. For example, they are compliant with GDPR and PCI-DSS certified to ensure maximum security for both the company and the guests.
The suitable MSP will listen to your full story, the current situation they’re in, their urgent needs, and the resources currently on hand. The pricing reflects exactly the services that the MSP is offering. Anything that's not agreed upon, or is not used, will be excluded from the price.
Businesses and MSPs should also openly discuss the nitty, gritty but critical details, such as how the quality and performance metrics will be met, list of liabilities in case of system shutdowns, the process in which how issues will be resolved as well as a detailed list of services and responsibilities on the MSP side.
And finally, a suitable MSP should be able to support the business anytime, anywhere.
Some executives may find the idea of keeping their data “in the cloud” risky. But cloud-based software is actually as safe as or even safer than on-premises software. It is not surprising given the fact that cloud service providers typically employ full-time teams of professionals who can provide far better security than any typical internal IT team can.
Cloud service vendors are independently audited and certified to ensure they comply with a wide variety of industry standards, including those concerning security.
Another aspect of cloud security is data recovery and redundancy. When your data is stored in the cloud, it is backed up regularly and often stored in several places. Most on-premises implementations may not have that level of redundancy.
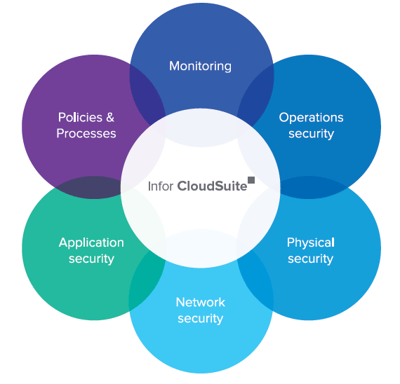
Here’s how a cloud service provider can protect your data from a host of evolving cyber security threats:
Data centres are the very foundation of cloud computing. As this is where all of the customers’ data is stored, data centres are critical assets for everyday operations.
The facility requires both human and technologies protection against cyber threats, illegal intrusion and natural disasters. Its top-notch security system will be discussed in the later part.
The perimeter layer comprises security guards, fences, threat detectors, and other security measures necessary tailored specifically to each location.
This layer of security also deals with authorising/ denying access and entry monitoring. Each access must have a reason, must serve a purpose, and is reviewed by designated personnel.
Those who frequently enter the data centres are only given entry to a specific area, and their access is routinely scrutinised, including the area access manager.
First and foremost, network security requires a secured architecture that has multiple layers. These layers are built to protect against both very specific attacks (e.g., DDoS) and more general information gathering attacks (e.g., vulnerability scanning). The implemented mechanisms have the ability to proactively defend against an attack, while also providing real-time monitoring of current threats from the Internet.
At no point is traffic within the network should be broadcasted from an antenna or wireless transmitter that would expose it to interception by third parties equipped for wireless snooping, now a sophisticated and accessible field.
The cloud service provider’s system has to be designed to maintain network security even when serving clients who don’t use best security practices. For example, the system would need to be protected from a user with a compromised system not running the latest anti-virus protection.
To ensure security is built into cloud service applications from the start, security requirements for each product are defined and then architected into the software design. Code reviews allow product teams to share secure coding practices they have gathered through own research or past implementations.
Strict data transmission protocols are rigorously enforced by using technologies such as SSL/TLS and transaction-based business logic.
Encryption is used extensively within the cloud service provider’s environment to ensure that data is protected. While in-transit, data is encrypted using appropriate mechanisms that include TLS/SSL, PGP, and secure FTP.
When required, data-at-rest is encrypted using database, file system, or other appropriate encryption capabilities.
The cloud service provider also maintains centrally managed passwords to protect administrative access points to the network, applications, and IT infrastructure. To defeat password cracking by brute force, the system registers unsuccessful password attempts and patterns, alerting network management staff to investigate.
Every secure session with a web server has an important aspect—the ability to authenticate the server. Certificates are the foundation of a secure cloud implementation, where each primary element of the cloud service solution presents a verifiable identity.
The cloud service provider must ensure customers own their data, and it is accessible at all times. Customers can also have all data returned at the end of the engagement.
The only network details collected by the cloud service vendor’s logging and auditing systems are application, system, and network logs and metadata. Log information that contains actual customer data must not be collected.
Whenever an application deals with data that requires regulatory compliance (e.g., HIPAA, SOX, PCI, GLBA, regional privacy laws, etc.), The cloud vendor works with customers to ensure that the controls needed to meet those requirements are in place.
In addition to cost savings, agility, and security, cloud services often come with unmatched capabilities regarding data backup, disaster recovery, and round-the-clock availability.
Your on-premises data is only as safe as your data centre / server room:
Disaster recovery, data backups and redundancy are all critical yet oftentimes overlooked IT tasks. They are like a good insurance policy. You do not want to use it regularly, or to use it at all, but you definitely need one.
While it is entirely possible to design, implement, monitor, and manage disaster recovery, backups and redundancy policies effectively on-premises, cloud computing services can deliver the same results more consistently and at a lower cost.
Here’s how AWS (Amazon Web Services) – the world largest cloud computing service provider – can achieve that through its widespread physical locations as well as the extensive global cloud infrastructures.
A data centre, in essence, is a physical facility that houses all the necessary IT equipment, such as servers, storage, network systems, routers, firewalls, etc. Also, a data centre includes non-IT elements like electrical switching, ventilation systems, backup generators, telecommunications, etc. The number of servers in each data centre can range from 50,000 to 80,000.
As this is where all of the customers’ data is stored, data centres are critical assets for everyday operations. The facility requires both human and technologies protection against cyber threats, illegal intrusion and natural disasters.
Each Availability Zone consists of several data centres. The main purpose of designating Availability Zones is to ensure all of AWS utmost critical components are always available, redundant and are in perfect working condition.
Each zone operates independently but is connected through fast, private fibre optic networking. The connection allows ease of transfer between Availability Zones from the same Region.
Each AWS Region houses multiple Availability Zones (the maximum number at the moment is 6 zone in one region, North Virginia). In addition to replicating the data between Availability Zones within the same region, clients can now choose to replicate across different locations and can leverage both public and private connectivity to guarantee their business will never be disturbed.
AWS currently has 55 Availability Zones across 18 geographic regions and planning to have more to further expand their service offers.
You can rest assured that even in the worst-case scenario, AWS will remain functional without a hitch. It's all thanks to the extra precautions, extreme care and diligent planning that put into establishing their data centres across the globe.
All equipment, machines, networks must undergo routine check-up, properly stored, and kept abundant in case of emergency. Generators are always available to power for the entire facility. The redundancy in equipment, power, water, telecommunications, internet connectivity, etc. ensures the power supply never goes interrupted or overheated.
Part of the AWS on-going security strategy is to test their security measures, responses, and equipment using simulations that mimic real-life emergencies. The employees are frequently trained so that they'll be able to rebound quickly and accurately when the time comes.
The high availability and extremely resilient systems enable the customers to achieve record recovery time and objectives, endless scalability, and free of error, unlike the traditional infrastructures.
Infor - the enterprise software giant from New York City, has gained tremendous popularity by offering deep industry-specific applications and suites, cloud deployment and extremely user-friendly interfaces. Though lesser-known among other software giants like SAP, Oracle and Microsoft, Infor has gained tremendous popularity by offering deep industry-specific applications and suites, cloud deployment and extremely user-friendly interfaces.
A portion of Infor's products is already cloud-based, such as Infor CloudSuite Industrial, a full-fledged enterprise resource planning application powered by Amazon Web Services.
Their CloudSuite solutions were designed with the customer in mind. These suites of solutions are packed full of the latest technological advances with intuitive user experience.
Amazon Web Services (AWS) provides a variety of cloud computing platforms and services on-demand to individuals, organisations as well as the governments. This subscription-based service offers a virtual computing power which can be accessed anytime as long as there is an internet connection, or in some cases, no connectivity at all.
Today, AWS has left their footprints in 190 countries. The widespread of physical locations as well as the extensive global cloud infrastructures enable businesses to deploy quickly, innovate regularly, scale on-demand. More importantly, companies now can do all of the above in a matter of a few hours, 24/7, instead of weeks or months like before.
TRG is an authorised cloud partner of AWS. We offer a wide range of cloud services to suit your specific needs. Whether you are a local SME or a global corporation, avoid making hefty upfront investments in hardware and spending tons of time and effort in managing it. Instead, get on-demand resources when you need and only pay for what you use with TRG’s cloud services.
During this once-in-century pandemic, many businesses have been able to transform and adapt, using the right technologies. Among these, cloud adoption is the most prominent trend, being embraced by an increasing number of companies regardless of size and industry.
As a result of profound disruptions caused by the ongoing COVID-19 crisis, TRG International would like to conduct a brief survey to understand your preferences and readiness in adopting cloud-based solutions for your business.
Finish this 3-minute survey now by clicking the button below.
From data warehousing to deployment tools, directories to content delivery, over 50 services are available in just a few mouse clicks with TRG's Cloud Services.
With TRG's Cloud Services, you will get on-demand resources when you need it and only pay for what you use with our cloud services.
Simply fill out the form on your right hand side to request a demo today!
Security is a major concern in our industry. Using Infor solutions was instrumental in ensuring we were delivering features with a high level of security and data privacy.

Howard Phung Fraser Hospitality Australia
TRG provides us with high-level support and industry knowledge and experience. There are challenges and roadblocks but it's certainly a collaboration and partnership that will see us be successful at the end.
Archie Natividad Aman Resorts
IT, Talent and F&B - we think it's a great combination.
We've thrived since 1994 resulting in lots of experience to share, we are beyond a companion, to more than 1,000 clients in 80+ countries.

© 2023 TRG International. Privacy Policy / Тerms & Conditions / Site map / Contact Us
TRG encourages websites and blogs to link to its web pages. Articles may be republished without alteration with the attribution statement "This article was first published by TRG International (www.trginternational.com)" and a clickable link back to the website.
We are changing support for TLS 1.0 and older browsers. Please check our list of supported browsers.